1. Do I need to install any prerequisite software before using PAM360?
Apart from the standard system requirements (both hardware and software), the following elements are essential for the proper functioning of the PAM360 server.
These are especially required if you are planning to make use of PAM360's account discovery and password reset provisions.
To check if these software requirements are configured:
Go to Support » Software Requirements and click Check Configuration.
In the pop-up box that opens, the configuration status will be displayed.
2. What are the operating systems supported by PAM360?
PAM360 supports the following flavors of Windows and Linux operating systems:
| Windows | Linux |
|---|---|
| Windows Server 2019 | Ubuntu 9.x and above |
| Windows Server 2016 | CentOS 4.4 and above |
| Windows Server 2012 R2 | Red Hat Linux 9.0 |
| Windows Server 2012 | Red Hat Enterprise Linux 7.x |
| Windows 10 | Red Hat Enterprise Linux 6.x |
| Windows 8 | Red Hat Enterprise Linux 5.x |
3. Can others see the resources added by me?
Except for super administrators (if configured in your PAM360 set up), no one including admin users, will be able to see the resources added by you. However, if you share your resources with other administrators, they will be able to see them.
4. Can I add my own attributes to PAM360 resources?
Yes, you can extend the attributes of the PAM360 resource and user account to include details that are specific to your needs. Refer this document for more details.
5. What happens if a user leaves the organization without sharing their sensitive passwords with anyone?
If an administrative user leaves the organization, they can transfer the resources they own to other administrators. By doing so, they'll have no access to those resources themselves, unless they transfer the resources to themselves. Refer this document for more details.
6. How to add a new Active Directory (AD) domain in PAM360?
Administrators can add new domains for both resource discovery and user discovery operations. Follow the below steps for resource discovery:
Refer to this help section for detailed instructions.
To add a new domain for user discovery:
Refer to this help section for detailed instructions.
7. How to remove a domain from PAM360?
To remove a domain from PAM360, you first need to remove the users that belong to this domain. Once the users are removed, follow the below steps to remove the domain information:
8. How to fix the errors “The list of Groups is too large to display ” and "The list of OUs is too large to display" while importing from AD?
To fix these errors, you need to increase the number of OUs and groups allowed during the AD import. Follow the below steps:
9. How can I edit the properties of an existing scheduled task, such as changing the time or the frequency?
You can modify the time interval for AD synchronization by following the below steps. To create a new task or edit the existing scheduled tasks, follow the below steps:
10. Can an AD sync job be set to occur multiple times a day, such as once every 4 hours?
Configuring a schedule to run every 4 hours must be done when you import the OU/Group from AD.
To import, go to Resources >> Discover Resources >> Import. Here, specify the synchronization interval as per your requirement and import.
11. How to fix the “PAM360 detected harmful content in the data entered by the user and aborted the operation" error occurred while importing resources through a csv/tsv file?
As a security measure, PAM360 to restricts certain characters such HTML tags (< , >), "URL: HTTPS://" or "URL: HTTP://", security mark (?), end line and multiple spaces in the notes or any other field in PAM360 to avoid causing security violations in the product.
If any of these characters are used in any other fields except the password field, then it causes a violation and the import fails.
To avoid this, verify your CSV/TSV file to ensure these characters are removed for a successful import.
12. How do I troubleshoot if importing users/resources from AD fails?
Verify the following:
If the above verifications fail, please contact pam360-support@manageengine.com.
13. Can I run custom queries to generate results for integration with other reporting systems?
Yes, you can. Please contact our support with your specific request and we will help you with the relevant SQL query to generate XML output.
14. Does domain SSO work across firewalls / VPNs?
The domain Single Sign On (Windows-integrated authentication) is achieved in the Windows environment by setting non-standard parameters in the HTTP header, which are usually stripped off by devices like firewalls / VPNs. PAM360 is designed for use within the network. So, if you have users connecting from outside the network, you cannot have SSO enabled.
15. Can I rebrand PAM360 with my own logo and organizational information?
Yes. PAM360 provides you with the following options for customization and rebranding:
To carry out the above functionalities:
Note that at any point, this configuration can be disabled. Know how.
16. Does PAM360 record Password viewing attempts and retrievals by users?
Yes, PAM360 records all operations that can be possibly performed by an user- including password viewing and copying operations. From audit trails, you can get a comprehensive list of all the actions and attempts by the users with password retrieval. Know more
17. Why does the size of PostgreSQL wal_archive file increase at a rapid pace?
This issue occurs when the backup location specified in PAM360 is no longer accessible to save the backup file. In simple terms, whenever the PostgreSQL database backup fails, wal_archive folder size will start increasing.
Solution:
This will trigger an instant backup and automatically purge the wal_archive directory.
18. Does PAM360 support High Availability?
Yes, refer the High Availability document for more details.
19. What are the various Syslog formats followed by PAM360?
The following are three different types of syslog formats that PAM360 uses to send syslog messages to your syslog collector host:
i. Resource Audit
ii. User Audit
iii. Key Audits
20. Does PAM360 alter the number of Windows CAL licenses?
Generally, RDP sessions are invoked from the PAM360 server and relayed to the end user's browser through a third-party component called Spark Gateway. This component comes bundled with PAM360 and does not have any relation to Windows CAL licenses. Hence, PAM360 does not affect the number of Windows CAL licenses in any way. Users need to purchase as many CAL licenses, as suggested by Microsoft.
21. How do I run the PAM360 service using a group Managed Service Account (gMSA)?
To know in detail about running the PAM360 service using a group Managed Service Account, click here.
22. How do I fix the PostgreSQL server start-up failure?
Error Scenarios:
During Upgrade:
'Trying to start PostgresSQL server failed' error in the command prompt after choosing the PPM file.
While setting up HA:
'Trying to start PostgresSQL server failed' error in the command prompt after executing the HASetup.bat command.
During Service Start up:
For the above two cases, do the following:
Open the <PAM360-HOME>\logs\wrapper file with notepad/Notepad++ and move to the very bottom of the file (i.e. most recent time frame) and check if we get the 'Trying to start PostgresSQL server failed' error.
Possible Causes:
The following causes are explained with respect to the above error scenarios:
The 'Trying to start PostgresSQL server failed' error occurs when,
Solution:
The solution given below applies to all the above error scenarios. To fix this issue, follow the below steps to provide permission,
If the issue still persists, zip and send us the logs from the <PAM360_HOME> and also the <PAM360-HOME>\pgsql\data\pg_log folder along with the above screen shots to pam360-support@manageengine.com.
23. How to handle the following exceptions that occur while upgrading PAM360 version?
Exception #1: Caused by: java.lang.OutOfMemoryError: GC overhead limit exceeded
If the issue still persists, please send your logs to pam360-support@manageengine.com for further investigation.
Exception #2: Trying to start the PostgreSQL server failed
24. How to perform version upgrade using the CLI mode?
Windows
Linux
Click here for detailed upgrade pack instructions.
25. Logs, Reports, and CAPTCHA are unreadable after a version upgrade. How to fix this issue?
Check for the following:
Use the following commands to install the dejavu fonts.
1. For RHEL / Centos:
sudo yum install fontconfig dejavu-sans-fonts dejavu-serif-fonts
2. Ubuntu / Debian:
sudo apt install fonts-dejavu fontconfig
3. SLES:
sudo zypper install dejavu-fonts fontconfig
Now, you have successfully installed the dejavu font in your machine.
After installing, follow the below steps:
1. Can I change the default port 8282 where PAM360 is listening?
Yes, you can change the default port as explained below:
2. How do I change the PAM360 web portal access URL?
This will serve as your custom web URL for PAM360 from now on.
3. PAM360 is a web-based application that can be accessed via a web browser. Does that mean I can access it from anywhere?
PAM360 is an on-premise tool installed in a physical server or virtual machines (VM). You can access PAM360's web interface from any machine on the network connected to the same LAN network using the web browsers.
4. Can I change the IP address in which PAM360 application is binding when I have multiple NIC cards and IP's available in the server?
PAM360 comes bundled with a tailored version of TomCat webserver which allows users to access the webpage and also the JVM which performs the product operations. You can use the below steps to configure the Bind IP address for both these components.
Steps for changing webserver bind IP
Steps for changing JVM bind IP
5. What if my users are not notified of their PAM360 accounts?
In general, users are notified of their PAM360 accounts only through emails. If a user does not get the notification emails, verify:
6. What are the authentication schemes available in PAM360?
You can use one of the following three authentication mechanisms out of PAM360:
Note:
For SAML SSO authentication, the Assertion Consumer URL is the hostname of the server, by default. To update the Assertion URL, follow the below steps:
Now, the Assertion Consumer URL under Service Provider Details will be updated.
7. What are the user roles available in PAM360? What are their access levels?
PAM360 comes with five pre-defined roles:
Apart from these default roles, any administrator can be promoted as a Super Administrator with the privilege to view and manage all the resources. Click here for details on the access levels of the default roles.
8. What if I forget my PAM360 login password?
If you were already given a valid PAM360 account, you can use the 'Forgot Password?' link available in the login page to reset your password. The username/email ID pair supplied should match the one already configured for the user. The password will be reset for that user and the new password will be sent to the respective email address. However, you wouldn't need this option if AD/LDAP authentication is enabled.
9. Why do I sometimes see a security warning while accessing the PAM360 console via the browser?
The PAM360 web console always uses the HTTPS protocol to communicate with the PAM360 server. The PAM360 server comes with a default self-signed SSL certificate, which the standard web browsers will not recognize, thereby issuing a warning. You can ignore this warning while you're testing or evaluating the product. However, if you're rolling it out in production, we recommend that you install an SSL certificate bought from an authorized Certificate Authority (CA) that is recognized by all standard web browsers. Know More
1. How secure are my passwords in PAM360?
Ensuring secure storage of passwords and offering solid defense against intrusion are the top priorities of PAM360. The following measures ensure high level security for your passwords:
2. How secure are Application-to-Application and Application-to-Database password management done through Password Management APIs?
PAM360 offers RESTful APIs and SSH-based CLI APIs that can be used for Application-to-Application/Database password management. The applications connect and interact with PAM360 through HTTPS. An application's identity is verified first by verifying the validity of its SSL certificate, and then by verifying the source IP/hostname in which it resides. Each application/database must be registered as an API User in PAM360. During this registration, the hostname/IP of the application server has to be supplied and a unique authentication token that uses the REST API will be generated. This token needs to be sent along with the API requests for authentication. In addition to these security checks, each application/database can only access the information that are explicitly delegated to them by an administrative user. Refer to this document to know more about sharing/delegating passwords.
3. Can we install our own SSL certificates?
Yes, you can install your own SSL certificates. Follow the steps below:
4. How to generate signed SSL certificates?
PAM360 runs as a HTTPS service. It requires a valid CA-signed SSL certificate with the principal name as the name of the host on which it runs. By default, on first time startup, it creates a self-signed certificate, which will not be trusted by the user browsers. Thus, while connecting to PAM360, you need to manually verify the certificate information and the host name of PAM360 server carefully and should force the browser to accept the certificate.
To make the PAM360 server trusted by web browsers and users:
There are different ways to generate the signed SSL certificates:
You can decide the mode of generating the signed SSL certificates based on what your security administrators recommend. The detailed steps for using each of the above methods are provided under the links below.
Note: If you already have a certificate signed by a CA, then we recommend using OpenSSL to create the keystore and configure it in PAM360 (steps 4 and 5 in the instructions below).
1. Generating Signed SSL certificates using the Certificate Management module of PAM360
You can generate signed SSL certificates through the Certificate Management module of PAM360 and also apply the certificate changes (Certificate Keystore) directly from the PAM360 console. This involves three processes:
1.1 Generating a Certificate Signing Request (CSR):
To request and acquire certificates from a Local CA through PAM360, you need to first generate a Certificate Signing Request (CSR). Here are the steps for the same:
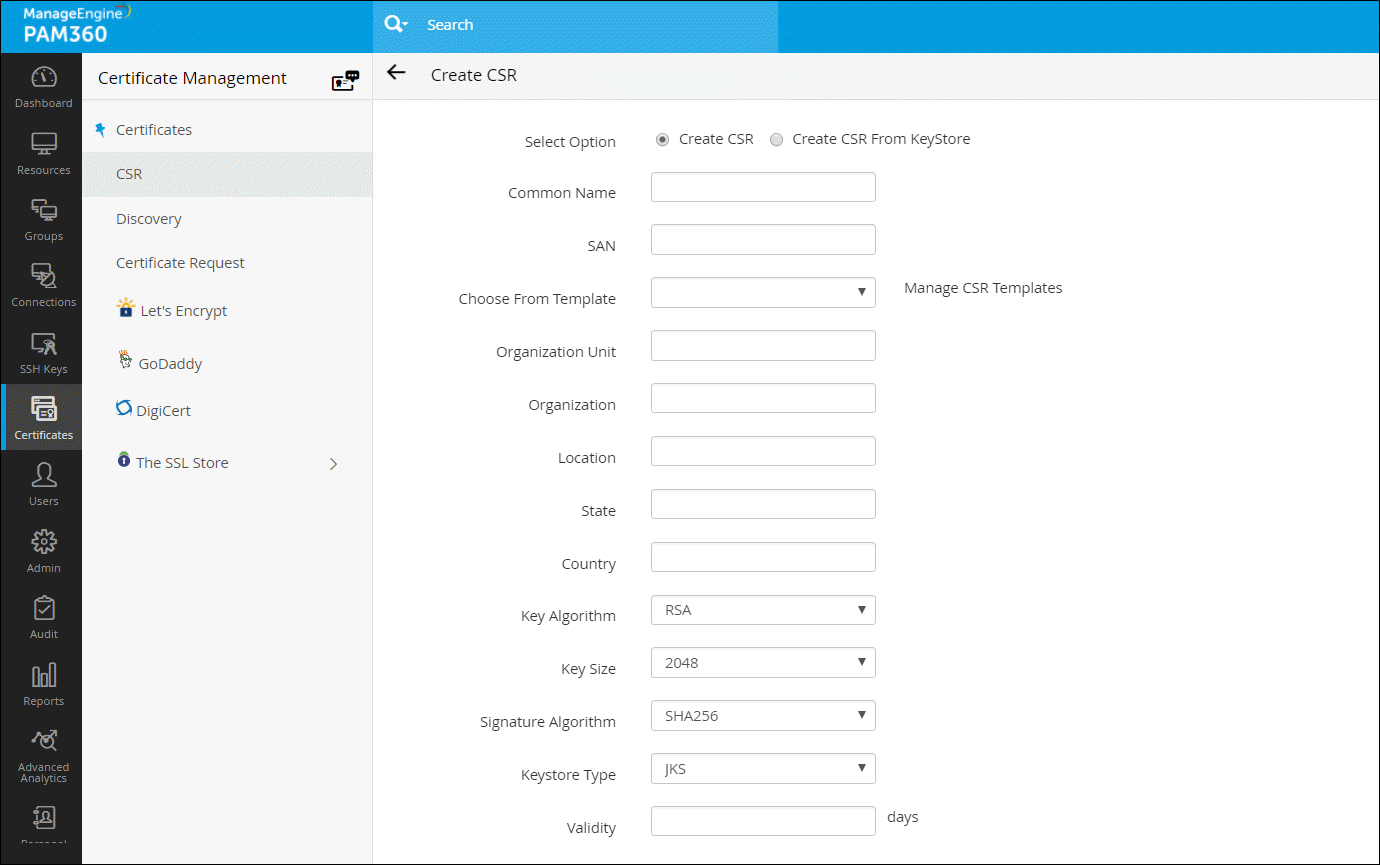
Note: The 'show passphrase' eye icon corresponding to each CSR allows the administrators to view the KeyStore passwords of the CSR files.
1.2 Signing the Certificate:
PAM360 provides the option to sign and issue certificates to all clients in your network either from your Microsoft Certificate Authority or using a custom root CA certificate that is trusted within your environment.
Note: Remember, you should have generated a valid Certificate Signing Request (CSR) before getting your certificate signed from the local CA.
Follow the below steps to sign the certificate:
1.3 Applying the Certificate Keystore for PAM360 web server:
To apply the certificate Keystore, first you need to create it.
2. Generating Signed SSL certificates using OpenSSL
OpenSSL mostly comes bundled with the Linux distributions. If you are using the Windows server and do not have OpenSSL installed, download it from http://www.slproweb.com/products/Win32OpenSSL.html. Make sure the 'bin' folder under the OpenSSL installation is included in the 'PATH' environment variable.
2.1 Create the public-private key pair that will be used for the SSL handshake
<privatekey_filename> is the filename you specify to store the private key.
2.2 Create a Certificate Signing Request (CSR) for submission to a certificate authority to create a signed certificate with the public key generated in the previous step
2.3 Submit the CSR to a Certificate Authority (CA) to obtain a CA signed certificate
Some of the prominent CAs are Verisign, Thawte, RapidSSL. Check their documentation / website for details on submitting CSRs and this will involve a cost to be paid to the CA. This process usually takes a few days time and you will be returned your signed SSL certificate and the CA's root certificate as .cer files. Save them both in the same working folder where files from steps 1 and 2 are stored
2.4 Import the CA-signed certificate to a keystore
where,
2.5 Configure the PAM360 server to use the keystore with your SSL certificate
This is the final step in generating Signed SSL certificates using OpenSSL.
3. Generating Signed SSL certificates using Keytool
3.1 Create the public-private key pair that will be used for the SSL handshake
where,
<keystore_password> is the password to access the keystore, <privatekey_password> is the password to protect your private key. Note that due to an inherent limitation in tomcat, these two passwords have to be the same. (Though it is not documented, Tomcat has issues with passwords containing special characters, so use a password that has only alpha characters)
<no_of_days> is the validity of the key pair in number of days, from the day it was created
3.2 Create a Certificate Signing Request (CSR) for submission to a certificate authority to create a signed certificate with the public key generated in the previous step
Note: The <csr_filename> that you choose should have the .csr extension.
3.3 Submit the CSR to a Certificate Authority (CA) to obtain a signed certificate
Some of the prominent CAs are Verisign, Thawte, RapidSSL. Check their documentation / website for details on submitting the CSRs. Please note that this is a paid service. This process usually takes a few days of time. You will receive your signed SSL certificate and the CA's certificate as .cer files. Save both the files in the <PAM360_Home>/jre/bin folder.
3.4 Import the CA-signed certificate to the PAM360 server
"keytool -import -alias PAM360 -keypass <privatekey_password> -storepass <keystore_password> -keystore <keystore_filename> -trustcacerts -file <your_ssl_bundle.p7b>"
where,
3.5 Configure the PAM360 server to use the keystore with your SSL certificate
This is the final step in generating Signed SSL certificates using Keytool.
Note: This step is applicable only if you're using the version 9700 or above.
Note: Tomcat, by default, accepts only the JKS (Java Key Store) and PKCS #12 format keystores. In case, the keystore is of PKCS #12 format, include the following option in the server.xml file along with the keystore name, keystoreType="PKCS12? This notifies tomcat that the format is PKCS12. Restart the server after this change.
4. Generating Signed SSL certificates by installing an existing wild card supported SSL certificate:
Note: Please refer your CA's documentation for more details and troubleshooting.
5. How to make the PAM360 server trusted by web browsers and users?
PAM360 runs as a HTTPS service. It requires a valid CA-signed SSL certificate with the principal name as the name of the host on which it runs. By default, on first time startup, it creates a self-signed certificate, which will not be trusted by the user browsers. Thus, while connecting to PAM360, you need to manually verify the certificate information and the host name of PAM360 server carefully and should force the browser to accept the certificate.
To make the PAM360 server trusted by web browsers and users:
There are different ways to generate the signed SSL certificates:
You can decide the mode of generating the signed SSL certificates based on what your security administrators recommend. The detailed steps for using each of the above methods are provided under the links below.
Note: If you already have a certificate signed by a CA, then we recommend using OpenSSL to create the keystore and configure it in PAM360 (steps 4 and 5 in the instructions below).
1. Generating Signed SSL certificates using the Certificate Management module of PAM360
You can generate signed SSL certificates through the Certificate Management module of PAM360 and also apply the certificate changes (Certificate Keystore) directly from the PAM360 console. This involves three processes:
1.1 Generating a Certificate Signing Request (CSR):
To request and acquire certificates from a Local CA through PAM360, you need to first generate a Certificate Signing Request (CSR). Here are the steps for the same:
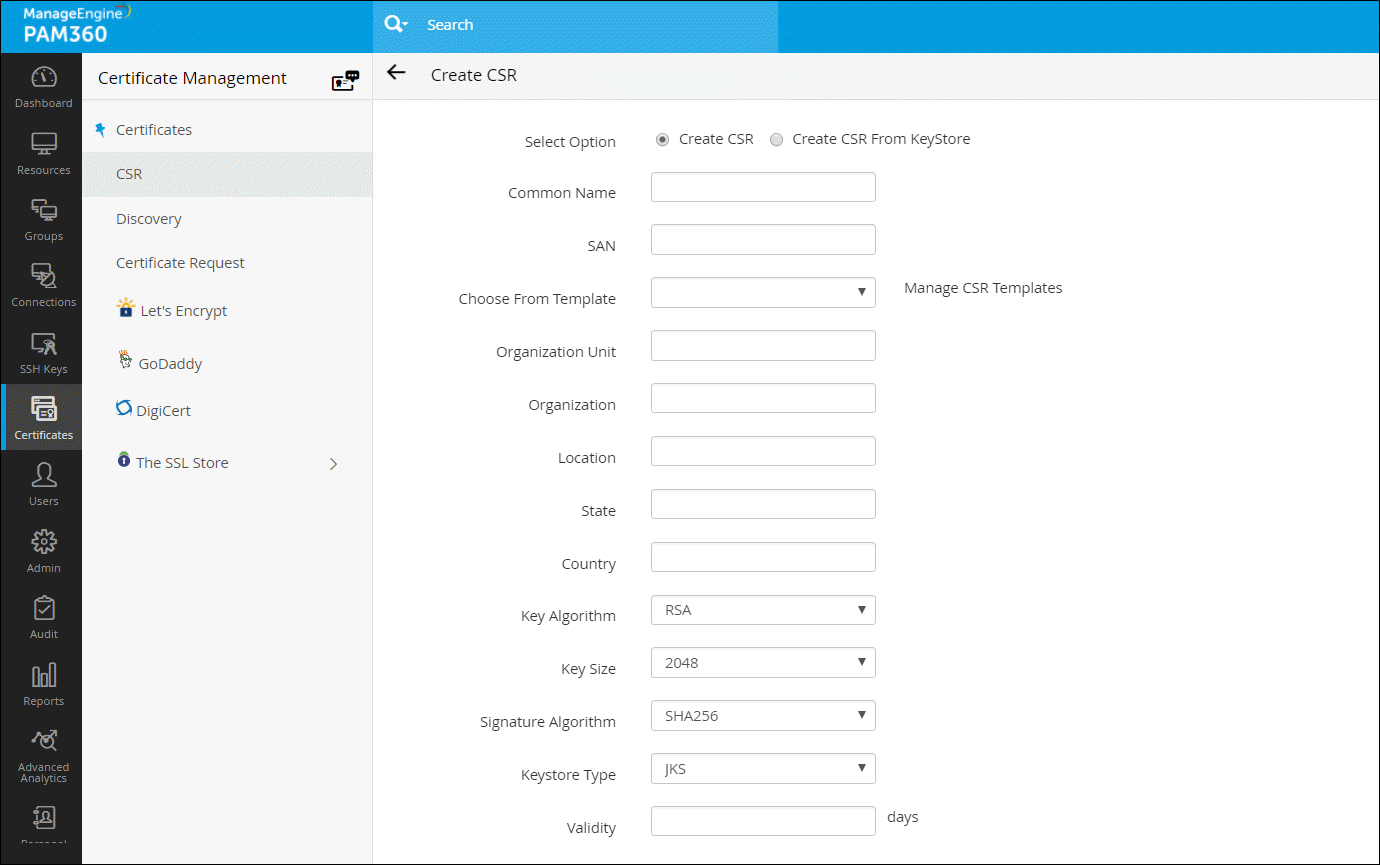
Note: The 'show passphrase' eye icon corresponding to each CSR allows the administrators to view the KeyStore passwords of the CSR files.
1.2 Signing the Certificate:
PAM360 provides the option to sign and issue certificates to all clients in your network either from your Microsoft Certificate Authority or using a custom root CA certificate that is trusted within your environment.
Note: Remember, you should have generated a valid Certificate Signing Request (CSR) before getting your certificate signed from the local CA.
Follow the below steps to sign the certificate:
1.3 Applying the Certificate Keystore for PAM360 web server:
To apply the certificate Keystore, first you need to create it.
2. Generating Signed SSL certificates using OpenSSL
OpenSSL mostly comes bundled with the Linux distributions. If you are using the Windows server and do not have OpenSSL installed, download it from http://www.slproweb.com/products/Win32OpenSSL.html. Make sure the 'bin' folder under the OpenSSL installation is included in the 'PATH' environment variable.
2.1 Create the public-private key pair that will be used for the SSL handshake
<privatekey_filename> is the filename you specify to store the private key.
2.2 Create a Certificate Signing Request (CSR) for submission to a certificate authority to create a signed certificate with the public key generated in the previous step
2.3 Submit the CSR to a Certificate Authority (CA) to obtain a CA signed certificate
Some of the prominent CAs are Verisign, Thawte, RapidSSL. Check their documentation / website for details on submitting CSRs and this will involve a cost to be paid to the CA. This process usually takes a few days time and you will be returned your signed SSL certificate and the CA's root certificate as .cer files. Save them both in the same working folder where files from steps 1 and 2 are stored
2.4 Import the CA-signed certificate to a keystore
where,
2.5 Configure the PAM360 server to use the keystore with your SSL certificate
This is the final step in generating Signed SSL certificates using OpenSSL.
3. Generating Signed SSL certificates using Keytool
3.1 Create the public-private key pair that will be used for the SSL handshake
where,
<keystore_password> is the password to access the keystore, <privatekey_password> is the password to protect your private key. Note that due to an inherent limitation in tomcat, these two passwords have to be the same. (Though it is not documented, Tomcat has issues with passwords containing special characters, so use a password that has only alpha characters)
<no_of_days> is the validity of the key pair in number of days, from the day it was created
3.2 Create a Certificate Signing Request (CSR) for submission to a certificate authority to create a signed certificate with the public key generated in the previous step
Note: The <csr_filename> that you choose should have the .csr extension.
3.3 Submit the CSR to a Certificate Authority (CA) to obtain a signed certificate
Some of the prominent CAs are Verisign, Thawte, RapidSSL. Check their documentation / website for details on submitting the CSRs. Please note that this is a paid service. This process usually takes a few days of time. You will receive your signed SSL certificate and the CA's certificate as .cer files. Save both the files in the <PAM360_Home>/jre/bin folder.
3.4 Import the CA-signed certificate to the PAM360 server
"keytool -import -alias PAM360 -keypass <privatekey_password> -storepass <keystore_password> -keystore <keystore_filename> -trustcacerts -file <your_ssl_bundle.p7b>"
where,
3.5 Configure the PAM360 server to use the keystore with your SSL certificate
This is the final step in generating Signed SSL certificates using Keytool.
Note: This step is applicable only if you're using the version 9700 or above.
Note: Tomcat, by default, accepts only the JKS (Java Key Store) and PKCS #12 format keystores. In case, the keystore is of PKCS #12 format, include the following option in the server.xml file along with the keystore name, keystoreType="PKCS12? This notifies tomcat that the format is PKCS12. Restart the server after this change.
4. Generating Signed SSL certificates by installing an existing wild card supported SSL certificate:
Note: Please refer your CA's documentation for more details and troubleshooting.
6. Can we create server certificates with SubjectAlternativeName (SAN)?
Yes, you can create a certificate using SAN with an alias name and apply it in PAM360. Follow the below steps:
1. Creating a CSR using PAM360's SSL certificate management module, and submitting it to any CA for signing
1.1 Create a Certificate Signing Request (CSR)
1.2 Submit the CSR to a Certificate Authority (CA) to obtain a CA signed certificate
After creating the CSR, the next step is get the CSR verified and signed by a CA. There are two options to do this:
Once signed, you can view the certificate under 'Certificates'.
1.3 Import the CA-signed certificate to the PAM360 server
To import the certificates in your network:
2. Creating a certificate with SAN using Microsoft internal CA
Make sure you follow the below mentioned steps to create server certificate with SubjectAlternativeName using Microsoft Internal CA. Also, in Additional Attributes, specify the 'san:dns=<The URL which you use to access PAM360>', and then try creating the certificate.
Notes:
For example,
./keytool -import -alias root1 -keypass Password123 -storepass Password123 -keystore PAM360.keystore -trustcacerts -file root1.cer
./keytool -import -alias root2 -keypass Password123 -storepass Password123 -keystore PAM360.keystore -trustcacerts -file root2.cer
Based on the number of root or intermediate root certificates, you have to execute the above command with different alias names and then continue with the actual certificate.
3. Creating certificate with SAN signed by third party vendor like GoDaddy, Verisign, Commodo, etc.
Make sure you follow the below mentioned steps to get SAN certificate signed from the third party vendors.
'./keytool -genkey -alias PAM360 -keyalg RSA -keypass <privatekey_password> -storepass <keystore_password> -validity <no_of days> -sigalg SHA256withRSA -keysize 2048 -keystore <keystore_filename>"'
Here, when it prompts for first and last name, specify the name which you use to access PAM360.
'keytool -certreq -keyalg RSA -alias PAM360 -keypass <privatekey_password> -storepass <keystore_password> -file <csr_filename> -keystore PAM360.keystore'
Note: If you receive the error message "Failed to establish chain from reply" with the above command. Then, the root and intermediate certs of your CA are not available in the trusted store of the PAM360. So, before importing the actual certificate, you have to import the root certificate with a different alias and then the actual certificate. Also, if you have multiple root certificates, then you have to import them one by one with different alias names. For example,
./keytool -import -alias root1 -keypass Password123 -storepass Password123 -keystore PAM360.keystore -trustcacerts -file root1.cer
./keytool -import -alias root2 -keypass Password123 -storepass Password123 -keystore PAM360.keystore -trustcacerts -file root2.cer
Based on the number of root or intermediate root certificates, you have to execute the above command with different alias names and then continue with the actual certificate.
1. Can I change resource passwords from the PAM360 console?
Yes. PAM360 can remotely reset the passwords of various end points. PAM360 supports both agent-based and agent-less modes of changing passwords. Refer this document for more information.
2. When do I use the agent and agent-less modes for password synchronization?
Let us first look at the requisites for both the modes:
The agent mode requires the agent to be installed as a service in each end point and run with administrative privileges to perform password reset operations. The agent uses one-way communication using outbound traffic to reach the PAM360 server.
For the agent less mode, you must supply administrative credentials to perform the password changes. For Linux, you must specify two accounts- one with root privileges and the other with normal user privileges that can be used to login remotely. Telnet or SSH service must be running on the resources. For Windows domain, you must supply the domain administrator's credentials. For Windows and Windows Domain, PAM360 uses remote calls, so relevant ports must be open on the resource.
Based on this, you can choose which mode you want for your environment, indicated by the following tips:
Choose the agent mode when:
Choose agent less mode in all other cases as it is a more convenient and reliable way of doing password changes.
3. Can I enable agent less password reset if I add my own resource type for other distributions of Linux / other versions of Windows?
Yes, you can. As long as your resource type label contains the string 'Linux' or 'Windows', you can still configure agent less password reset for those resources.
Example of valid resource type labels to enable password reset:
Debian Linux, Linux - Cent OS, SuSE Linux, Windows XP Workstation, Windows 2003 Server
4. Is there a way to carry out remote password synchronization for custom resource types that do not come out of the box in PAM360?
PAM360 supports remote password reset for custom resource types through SSH command sets, password reset plugins, and password reset listeners.
5. How do I troubleshoot when password reset does not happen?
In the agent mode:
In the agent less mode:
6. How do I reset domain passwords when Windows domain password reset fails with an error message: "The authentication mechanism is unknown"?
This happens when PAM360 is run as a Windows service and the 'Log on as" property of the service is set to the local system account. Change it to any domain user account to be able to reset domain passwords. Follow the instructions below to effect that setting:
7. What are the prerequisites for enabling Windows Service Account Reset?
Before enabling windows service account reset, ensure if the following services are enabled in the servers where the dependent services are running:
8. Does domain SSO work across firewalls / VPNs?
The domain Single Sign On (windows integrated authentication) is achieved in the Windows environment by setting non-standard parameters in the HTTP header, which are usually stripped off by devices like firewalls / VPNs. PAM360 is designed for use within the network. So, if you have users connecting from outside the network, you cannot have SSO this enabled.
1. Can I move PAM360 from one server to another?
Yes. you can migrate PAM360 to another server by following the below steps:
2. Can I setup disaster recovery for the PAM360 database?
Yes, you can. PAM360 can periodically backup the entire contents of the database, which can be configured through the PAM360 console. Refer this document for more details.
3. Where does the backup data get stored? Is it encrypted?
All sensitive data in the backup file are encrypted using the 7-Zip utility, which has options to encrypt and compress data by the AES256 algorithm. The encrypted data is stored under the '<PAM360_Install_Directory/backUp>' directory as a .zip file. We recommended you to store the backup in secure, secondary storage for disaster recovery.
1. What is the Licensing Policy for PAM360?
There are three license types:
Note: PAM360 comes with five user roles - Administrator, Password Administrator, Privileged Administrator, Password Auditor and Password User. The term 'administrator' denotes Administrators, Password Administrators and Privileged Administrators. So, licensing restricts the number of administrators as a whole, which includes Administrators, Password Administrators and Privileged Administrators. There is no restriction on the number of Password Users and Password Auditors. To get more details on the five user roles, refer this section of our help documentation.
2. Can I buy a permanent license for PAM360? What are the options available?
Though PAM360 follows an annual subscription model for pricing, we also provide perpetual licensing option. The perpetual license will cost three times the annual subscription price, with 20% AMS from the second year. Contact sales@manageengine.com for more details.
3. How can I apply my license file?
4. I want to have a High Availability setup with multiple servers. Will a single license suffice for this?
Yes, if you buy a single license, you are entitled to have the High Availability setup. You can apply the same license on the Primary as well as the Secondary servers. Follow the below steps:
5. Can PAM360 support more than 1000 administrators?
Yes, very much. If you want a license with more than 1000 administrator users, please contact sales@manageengine.com for more details.
6. Can I extend my evaluation to include more administrator users or for more number of days?
Yes. Fill in the required details in the website and we will send you the license keys.
1. Are there any differences in the way SSH user accounts and SSH service accounts are managed using PAM360?
No. PAM360 adopts the same approach for managing SSH user accounts and SSH service accounts. The only difference is that during resource discovery, if service / root account credentials are provided to establish connection with the resource, you acquire extended privileges to import and manage keys from all user accounts in the resource.
Whereas, when connection to the resource is established using user account credentials, you get key management privileges only for SSH keys present in that particular account.
2. Is there any way to view SSH keys that were not rotated?
Yes. We have a dashboard that displays the number of keys that were not rotated for the predefined time period as specified in the notification policy.
3. Does PAM360 support management of digital keys other than SSH keys and SSL certificates?
PAM360 houses a key vault called "Key Store" which facilitates the storage and management of any type of digital key. However, the option to discover and import is limited to SSH keys and SSL certificates only, and isn't available for other types of digital keys.
1. Is there any certificate type that PAM360 is incompatible with?
No. PAM360 supports all X.509 certificate types.
2. Is it possible to automatically identify and update the latest version of certificates in PAM360' certificate repository?
Yes. You can create scheduled tasks to perform automatic certificate discovery through which you can import and replace old certificates from target systems with their updated versions in PAM360' certificate repository. Click here for a detailed explanation on creating schedules.
3. Does the Linux version of PAM360 support certificate discovery from Active Directory and MS Certificate Store?
No, it doesn't. The AD User Certificate and MS Certificate Store tabs appear only in the Windows version of PAM360.
4. Is it possible to track the expiry of certificates with the same common name in PAM360' certificate repository?
PAM360 differentiates certificates by their common names and records certificates with same common names as a single entry in its certificate repository. We've designed it this way because PAM360 licensing is based on the number of certificates and we don't want customers to spend many license keys for the same certificate.
However, if there's a need to manage both the certificates separately, you can do so by listing them as separate entries in PAM360' certificate repository. Once listed, the newly added certificate will be counted for licensing.
To add a certificate with the same common name as a separate entry in certificate repository,
5. How do I import private key for a certificate?
Follow the steps below to import a certificate's private key into PAM360.
Browse for the file that contains the private key, enter the keystore password, and click on 'Import'. The private key will be imported and attached to the selected certificate.
6. How do I deploy a certificate to Certificate Store and map it to the application that uses the certificate?
PAM360 facilitates certificate deployment through which you can deploy certificates from its repository to target server's Microsoft Certificate Store.
Click here for step-by-step explanation on certificate deployment.
To map the certificate to its corresponding application, you've to manually restart the server on which the application is running for the change to take effect.
7. Does PAM360 support subnet based certificate discovery?
No. PAM360 currently doesn't support subnet based SSL certificate discovery.
8. Does PAM360 support automatic scheduling for certificate discovery from MS Certificate Store?
No. Currently, PAM360 doesn't support automatic scheduling for certificate discovery from MS Certificate Store.
9. Are certificate related alert emails generated for all versions of a certificate (the ones that show in "Certificate History" also) or only for those certificates listed in PAM360's certificate repository?
Email notifications are generated ONLY for certificates listed in PAM360's certificate repository and NOT for different versions of a certificate displayed in "Certificate History" section.
10. Are the certificates issued by the company's internal Certification Authority (CA) counted for licensing?
Yes. All types of SSL certificates, SSH keys and any other digital key being managed using PAM360 are taken into account for licensing. There's a dashboard widget "License Details" that provides insights on the type and number of digital identities being managed using PAM360 that will be taken into account for licensing.
11. How do I import a root certificate into PAM360?
To import a root certificate, open the Command Prompt and navigate to the <pam360_server_home>\bin directory and execute the following command:
For Windows:
importCert.bat <Absolute Path of certificate>
For Linux:
importCert.sh <Absolute Path of certificate>